
The Economics of Clop’s Zero-Day Campaigns: Why Mass Exploitation Isn’t Paying Off
What is this About?
Clop, also known as “Cl0p”, is a data extortion group that has operated since 2019. It has long been something of an outlier among its peers. Although the group began its operations with more commonplace double-extortion ransomware attacks typical in the ransomware ecosystem, it quickly gained notoriety for data extortion-only campaigns. Most groups use a variety of methods to enter victim networks – including phishing and credential theft. Instead, Clop gained initial access by exploiting novel zero-day vulnerabilities on commercial file transfer and storage solutions. Rather than attack in the same place defenders knew to look, Clop attacks came up in places no one realized were vulnerable, and the ubiquity of the software programs meant that any organization could be next.
The group has capitalized on these vulnerabilities to enter hundreds of victim networks in a relatively short amount of time. Each of their campaigns leading to a score of victim claims on their data leak site. While Clop can point to impressive victim counts and data volumes, their extortion-only approach inflicts less operational harm than ransomware variants that encrypt systems and force business shutdowns.
This blog explores what we can learn from Clop’s activities and whether the group is more profitable than their double-extortion peers in the ransomware ecosystem.
Clop’s Campaign History
The first campaign that set Clop apart from its peers was in late 2020 through early 2021. This campaign targeted the Accellion File Transfer Appliance (FTA). Clop exploited several zero-day vulnerabilities within FTA, including the SQL injection vulnerability CVE-2021-27101. This allowed Clop to breach over 300 FTA tenants and steal victims’ data.
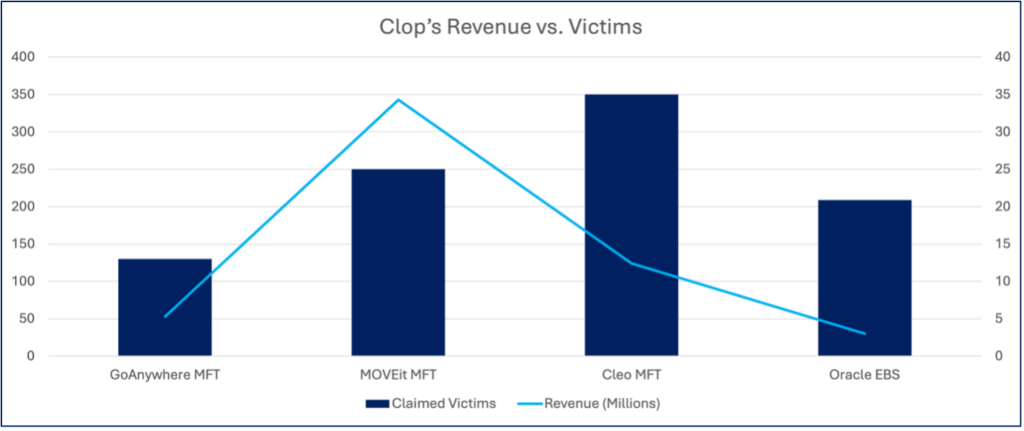
Clop’s next major campaign was in early 2023, where they set their sights on Forta GoAnywhere Managed File Transfer (MFT) software. Again, Clop was able to achieve access to MFTA environments via a zero-day vulnerability. This time, the group was able to achieve remote code execution (RCE) via exploitation of the command injection vulnerability CVE-2023-0669. Despite claiming to have impacted more than 130 victims on their dark web data leak site (DLS), we have only identified three confirmed transactions associated with the campaign, coming in at approximately $5.3 million in total.
Clop’s next foray targeted Progress Software’s MOVEit Secure Managed File Transfer solution in mid-2023. This was much more widespread in terms of victim volume than the previous two campaigns. Here, Clop again exploited a SQL injection zero-day vulnerability (CVE-2023-34362) in order to deploy a web shell in over 250 MOVEit environments. This campaign netted the group at least $34.3 million from six confirmed transactions, with the largest transaction alone coming in at $10 million USD. In early 2025, the group targeted Cleo’s Managed File Transfer (MFT) software. Over 350 organizations were named on Clop’s data leak site throughout the year. Clop again exploited the unrestricted file upload and download zero-day vulnerability CVE-2024-50623, gaining “write” privileges on Cleo appliances before executing PowerShell commands to employ a webshell, which has been dubbed “LEMURLOOT.” Despite having a higher victim count than their previous campaign, the group only took in $12.4 million from nine confirmed transactions, averaging out to approximately $1.4 million per payment. This reduced return on investment and reduced average payment may signal challenges in their extortion model.
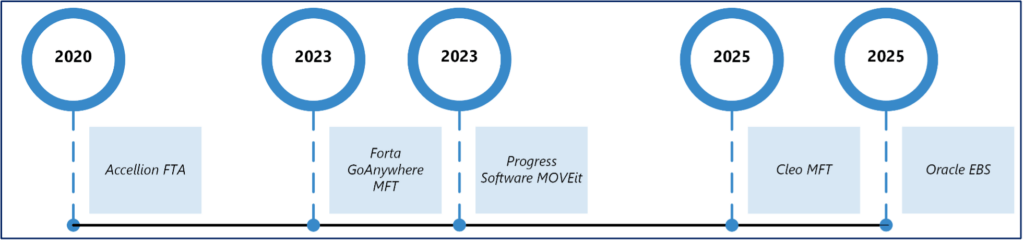
Timeline of Clop’s Exploitation Campaigns
The Oracle EBS Campaign
Late 2025 brought yet another Clop extortion campaign, this time targeting Oracle’s E-Business Suite (EBS). Clop was able to access victims’ EBS tenants, likely from exploiting CVE-2025-61882, which enables remote code execution. After compromising vulnerable devices, Clop deployed web shells for persistence and data exfiltration.
At the time of writing (March 2026), Clop claims it had access into over 234 victim’s EBS environments. Clop has continued publishing new victims to their DLS as recently as February 14th, 2026. The actual intrusions may have dated back to as early as July 2025, per Mandiant’s analysis.
Clop maintained a significant delay between data exfiltration and victim notification. While the operational rationale for this dwell time is not definitively known, it may serve tactical purposes. Potential tactical possibilities include organizing data from hundreds of victims or waiting for logs to roll over on EBS appliances, effectively hiding intrusion evidence. This delay between intrusions and victim notification has been consistent across several of Clop’s campaigns.
Additionally, the emails sent to victims were abrupt, instructing users to contact Clop at one of two email addresses. Notably, the email body explicitly acknowledged the exploitation of an Oracle E-Business Suite vulnerability.
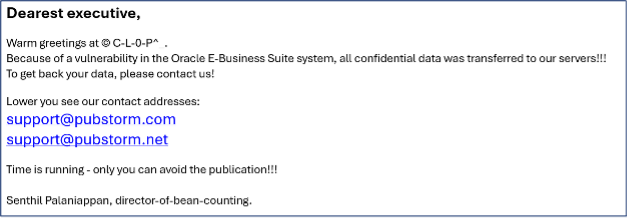
Example of extortion email sent to victims
Once a victim contacted one of the listed email addresses, they were directed to a dark web chat site operated by the threat actor. Based on our interactions with the group following this campaign, Clop exfiltrated substantial amounts of data — in one instance claiming multiple terabytes. The ransom demands matched the high volumes of data. Some initial extortion demands exceeding $10 million for data deletion. The group provided what it purported were complete lists of exfiltrated data and allowed victims to request sample files to verify their claims. Despite this substantial operation affecting over 100 victims, the financial outcome proved far less lucrative than the scale might suggest.
Evaluating Clop’s Extortion Model
GRIT only observed one confirmed ransom payment from the Oracle EBS campaign, which totaled $3 million. While substantial, it takes time, effort, and resources to organize, verify, and extort hundreds of organizations. Against the 234 claimed victims, this yields approximately $12,800 per breach, which makes it a poor return considering the operational investments required. Clop’s investments likely included:
- Procuring or developing the Oracle EBS zero-day exploit
- Triaging and organizing multi-terabyte datasets from hundreds of organizations
- Verifying data integrity and relevance for each victim
- Negotiating with dozens of potential targets
- Sustaining infrastructure capable of hosting and seeding terabytes of stolen data via torrents.
Most ransomware victims — Clop’s or otherwise — do not pay. Therefore, to maintain extortion pressure, Clop must make stolen data publicly accessible on their DLS to demonstrate credibility and follow-through on threats. While the group uses torrents to distribute hosting costs across seeders, they must initially host each victim’s complete dataset, which is often multiple terabytes, on their own infrastructure. This creates substantial costs: high-capacity storage servers, significant bandwidth for initial uploads and downloads, and ongoing operational security to prevent law enforcement takedown. Each terabyte uploaded requires substantial bandwidth and exposes their infrastructure to detection. Hosting costs alone pose a significant financial burden, as maintaining infrastructure capable of distributing hundreds of terabytes erodes potential profits. Beyond operational expenses, the group must also secure zero-day exploits, either by purchasing them from vulnerability brokers at premium prices or investing in the specialized expertise required for in-house development.
The Encryption Advantage: Comparing Clop to Akira
We recently analyzed ransom payments for the two most active groups of 2025, Qilin and Akira, in our annual GRIT 2026 Ransomware and Cyber Threat Report (I highly recommend checking this one out when you’re done with this blog), which is a useful point of comparison for Clop’s activity. Akira also weaponized a zero-day vulnerability as a primary driver of a wide-scale ransomware campaign in 2025 with relative financial success.
From our analysis, Akira has much more leverage in its operations than Clop because its business impacts are more severe. Akira targets and encrypts business critical servers that impact daily operations. Akira’s finances reflect this. The group generated more than $73 million dollars from ransom payments in 2025, dwarfing Clop’s ~$15 million payout from the Cleo and EBS exploitation attacks combined.
This disparity is particularly notable given that Clop previously operated as a traditional ransomware group with encryption capabilities. Their pivot to data-theft-only operations, although having enabled rapid, large-scale exploitation, has resulted in significantly diminished financial returns compared to groups that maintain encryption-based leverage. Although we are comparing Clop to one of 2025’s most prolific threat groups here, we believe that Clop’s diminished returns stem partly from their strategic shift away from encryption. Clop’s “smash and grab” method allows them quick entry to victim environments in a scalable way, but this method may not be optimal for its goals. Data generates less urgency in victims in comparison to the double extortion attacks that first emerged in 2019. From our experience working with victims of these attacks, we have seen that a victim’s legal obligations do not change whether a threat actor does or doesn’t publicly share data online. (Note: I am not a lawyer, and this is not legal advice). The National Crime Agency’s (NCA) Operation Cronos in 2024 revealed that ransomware actors don’t always delete data even after payment. Because of these factors, in most circumstances, paying solely for data suppression may not be advisable in ransomware attacks – Clop’s or otherwise.
Looking Ahead
Clop may continue their current approach of exploiting zero-days at scale for limited returns. The data-theft-only model provides operational benefits:
- Faster exploitation cycles
- Ability to target hundreds of victims simultaneously without complex ransomware deployment
- Reduced attack surface for detection by EDR solutions.
Additionally, some legal frameworks treat data theft less severely than operational disruption, potentially reducing legal risk. However, the group could also reintroduce encryption capabilities to increase leverage. Similarly, other ransomware groups may experiment with data-theft-only campaigns, but the lack of immediate business impact results in significantly lower payment rates compared to double-extortion operations.
How Organizations Can Defend Against Mass Exploitation
If history is any indicator, Clop will certainly try to target another commercial file transfer solution again. I’d be remiss if I didn’t mention a few ways to easily combat Clop and the scourge of data extorsion. That way, when Clop exploits the next zero-day, you can be properly prepared.
- Ensuring that file transfer solutions have appropriate data retention and cleanup polices can limit the data an actor is able to access should the worst-case scenario occur. Keeping this data in a secure location outside of the MFT can be a simple solution to keeping it off perimeter devices.
- Implementing IP-based allow lists for file transfer solutions can limit who can access these applications. While many of these products are open to the internet by design, limiting their access whenever possible (such as in B2B applications) can prevent bad actors from accessing them.
- Robust vulnerability management practices can’t stop every zero-day from being exploited, but they can ensure that old and outdated exploits aren’t weaponized. GreyNoise has found that over 40% of exploited vulnerabilities are four years are older, meaning that even basic vulnerability management practices can prevent a large swath of exploitation attempts.
- Multifactor Authentication (MFA) on every possible login portal can prevent attacks from abusing stolen credentials, whether those be from exploitation (like Akira’s SonicWall activities and potential future Clop exploits), or information stealing malware. MFA also can also mitigate damages done from brute force attacks against endpoints in the event a threat actor is able to successfully “stuff” credentials. It is a small extra step for users that has major security benefits.
- Endpoint Detection and Response (EDR) solutions deployed across all endpoints minimize impact when intruders gain network access. EDR solutions provide superior protection compared to traditional antivirus by analyzing behavior patterns rather than relying solely on file signatures. While Clop typically limits activity to compromised file transfer appliances without lateral movement, other threat actors routinely pivot to additional systems following initial compromise.
Thanks for reading, and happy hunting!
Note
I wanted to give a huge thank you to our friends at TRM Labs for allowing us access to their resources and insights that enabled us to analyze blockchain transactions in relation to ransomware infrastructure.