MICROSOFT SECURITY SERVICES
Maximize Your Microsoft
Security Investment
GuidePoint Security helps organizations unlock the full potential of Microsoft tools. With expert guidance, we help transform underutilized capabilities into measurable security outcomes.
THE MICROSOFT SECURITY CHALLENGE
Secure More With Existing Tools
Despite comprehensive Microsoft security licenses, resource constraints and competing priorities often leave powerful features underutilized, creating security gaps. Meanwhile, security threats continue to evolve.
Our Microsoft Security Services are designed to:
Uncover Gaps
Identify underutilized tools and redundant coverage
Design for Efficiency
Create tailored, scalable security architectures
Build for Outcomes
Deploy optimized solutions aligned with business priorities
Improve Posture Continuously
Measure progress and enhance ongoing protection
EXPERT-LED MICROSOFT SECURITY SERVICES
Expert Guidance. Measurable Results.
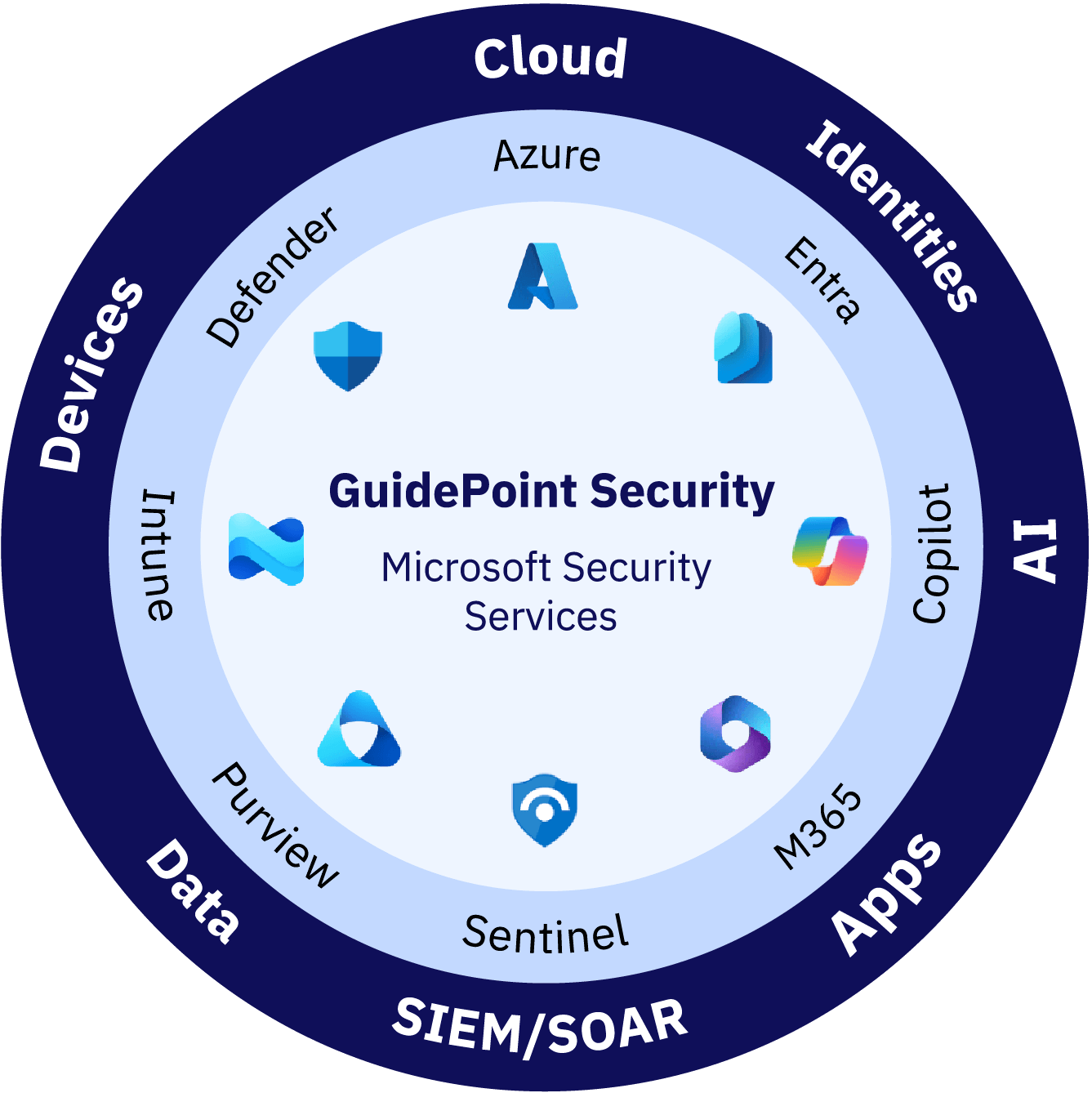
With rapid, diverse compute technology adoption comes increased pressure to secure complex environments at speed and scale. Our certified consultants bring deep Microsoft expertise and hands-on experience securing clouds, devices, applications, identities and artificial intelligence (AI) applications. As a certified Microsoft Solutions Partner for Security, we deliver proven guidance, seamless integration and measurable outcomes that strengthen an organization’s security posture.
Microsoft Cloud Security
Secure Microsoft cloud infrastructures with services that unlock comprehensive protection and visibility. GuidePoint helps organizations maximize the value of Microsoft Defender for Cloud, Azure Policy and Microsoft Sentinel so they can achieve unified security management, threat detection and compliance monitoring.
- Assessment Services for Microsoft Defender for Cloud: Identify configuration gaps and map to industry benchmarks.
- Architecture Services for Microsoft Sentinel and Azure Police: Unify visibility for a comprehensive cloud security strategy.
- Deployment Services for Microsoft Defender for Cloud and Azure Key Value: Create custom policies and achieve secure secrets management.
- Optimization Services for Microsoft Sentinel and Azure Policy: Continuously optimize playbooks and refine controls based on evolving threats.
Endpoint and Device Security
Protect endpoints with services designed to safeguard diverse, connected and distributed architectures. We ensure Microsoft Intune and Microsoft Defender solutions create comprehensive device security strategies that prevent, detect and respond to threats.
- Discover Opportunities to Fine-tune Microsoft Defender: Find unmanaged devices, expose device vulnerabilities and evaluate endpoint security gaps.
- Design Security-first Solutions for Microsoft Intune: Create a secure-by-design device connectivity architecture.
- Build Stronger IoT and Endpoint Protections: Let GuidePoint implement and optimize Microsoft Defender for Endpoint and IoT solutions that integrate threat defense into every connection.
- Enhance Device Security: GuidePoint refines Microsoft Intune policies and automates threat response for security that continuously improves.
Application Security
Improve SaaS security with Microsoft services from GuidePoint. We help extract greater value from Microsoft Defender for Cloud Apps, Microsoft Purview and integrated security features to protect your SaaS environment. This ensures comprehensive visibility and control across cloud application ecosystems.
- Identify SaaS Security Risks: We conduct comprehensive SaaS security posture assessments with Microsoft Defender for Cloud Apps.
- Architect SaaS Security Controls: Our services help customers unify protection, getting more value from their Microsoft Purview and Microsoft Defender for Cloud App licenses.
- Build and Integrate Custom Security Policies: We help organizations protect data within application environments using Microsoft Defender for Cloud Apps and Microsoft Purview.
- Optimize SaaS Security: Our security experts help customers continuously improve monitoring, refine policies and integrate workflows for maximum protection.
Identity Security
GuidePoint helps organizations implement best practices so they can strengthen identity foundations with Microsoft Entra ID (formerly Azure AD), Conditional Access and Privileged Identity Management.
- Identify Identity Security Gaps: We help organizations assess identity security and privileged access with Microsoft Entra ID Access Reviews.
- Architect Best-practices Identity Controls: GuidePoint configures policies for Microsoft Entra ID and Conditional Access.
- Implement Privileged Identity Management and Multi-factor Authentication (MFA): We help organizations build secure access on top of Microsoft Entra ID Protection MFA.
- Enhance Identity Security: Our regular Microsoft Conditional Access reviews and policy refinement help organizations stay ahead of changing and growing identity landscapes.
Data Security
Protect sensitive data wherever it lives with services for Microsoft’s integrated data security and compliance solutions. GuidePoint helps organizations leverage Microsoft Purview, Microsoft Defender for Cloud, Azure Information Protection and Data Security Posture Management (DSPM) to help define and operationalize end-to-end visibility, classification and protection for the most critical information assets.
- Assess Data Risk and Classification Gaps: Assessment services for Microsoft Purview Information Protection, sensitivity label analytics and DSPM discovery capabilities identify issues before they become data leaks.
- Architect a Unified Data Security Framework: Our engineers help organizations leverage Microsoft Purview Data Loss Prevention (DLP), Defender for Cloud and DSPM for cross-environment protection.
- Build a Secure Data Foundation: We help implement data encryption, labeling and access governance with Microsoft Information Protection, Azure Key Vault and DSPM validation for secure key management.
- Optimize Data Security: We offer services that help continually improve posture through Purview policy refinement, adaptive DLP tuning and DSPM-driven risk prioritization based on user behavior and threat insights.
SIEM / SOAR
Gain complete visibility and accelerate response with services that help maximize Microsoft’s advanced SIEM and SOAR capabilities. We help organizations streamline threat detection, investigation and automated response across hybrid environments using Microsoft Sentinel and Defender XDR.
- Find Coverage Gaps: Our assessments review your Microsoft Sentinel implementation, providing insights into security events, log coverage and data connectors.
- Architect a Scalable SIEM/SOAR Strategy: We help maximize the value of Microsoft Sentinel and Defender XDR with architectures that centralize visibility and response orchestration.
- Accelerate Incident Containment: We help build Sentinel analytics rules, playbooks and automation runbooks to reduce alert fatigue and speed incident containment.
- Optimize SOC Operations: GuidePoint provides continuous Sentinel rule tuning and integration with Microsoft Defender Threat Intelligence for real-time insight.
Artificial Intelligence
Enhance security resilience and operational efficiency with services for AI-driven Microsoft solutions. GuidePoint helps organizations harness Microsoft Copilot, Defender XDR and Sentinel’s machine learning models to detect threats faster, reduce noise and augment analyst decision-making.
- Assess AI Maturity and Readiness: With structured Microsoft Copilot readiness workshops, we help organizations determine their readiness and outline opportunities for AI-driven automation.
- Architect AI-powered Threat Detection and Response: We help organizations design strategies that integrate Copilot and Microsoft Sentinel and Defender XDR for faster, more intelligent security.
- Implement AI-assisted Investigation Workflows: GuidePoint builds natural-language queries and automated reporting to streamline SOC efficiency.
- Optimize AI Models and Playbooks: Our services continuously review AI analysis and telemetry against user feedback and emerging threat patterns to help organizations validate and improve AI-driven defenses.
MICROSOFT COPILOT SERVICES
Securely Harness the Potential of Microsoft Copilot
GuidePoint helps organizations ensure robust security, compliance and governance around Microsoft Copilot. With robust security, organizations can maximize AI productivity gains and innovation potential while minimizing risk.
- Comprehensive Security Evaluation: Assess AI model security, data protection mechanisms and access controls to identify and mitigate risks before deployment.
- Compliance Readiness: Validate the environment against regulatory requirements and establish governance frameworks tailored to AI-powered workloads.
- Strategic Implementation Planning: Develop a roadmap for secure Copilot integration that aligns with business objectives and security posture.
- Risk Mitigation: Identify potential vulnerabilities in Copilot architectures and establish controls to protect sensitive data and prevent unauthorized access.
- Adoption Optimization: Maximize ROI by ensuring the organization is technically and operationally prepared to leverage Copilot’s full capabilities securely.
MICROSOFT ECIF SERVICES
Unlock Microsoft ECIF to Fund a Stronger Security Journey
We streamline the Microsoft End Customer Investment Funds (ECIF) process and help accelerate funding for GuidePoint engagements while organizations focus on their core priorities. Our experts identify high-impact opportunities, manage program applications, maximize license value and handle reporting, transforming ECIF into a catalyst for security transformation.
- Get Funding Faster: We help manage the ECIF application process from start to finish.
- Maximize Investment Impact: We align customer security goals with Microsoft’s strategic priorities.
- Deliver Measurable Outcomes: GuidePoint experts implement solutions that demonstrate clear ROI.
- Simplify Reporting Requirements: We handle documentation to maintain ECIF compliance.

MICROSOFT SECURITY SERVICES METHODOLOGY
A Proven Path to Microsoft Security Optimization
Our Microsoft Security Services follow a proven methodology that meets organizations where they are, addresses unique business challenges and delivers continuous improvement for a secure future.
From identifying hidden vulnerabilities and tool gaps to designing tailored architectures, implementing optimized configurations and continuously enhancing your protection, our end-to-end services ensure customers extract maximum value from their Microsoft investments.
Discover
- Architecture, workload and security reviews
- Security health checks
- Identity reviews
- Posture evaluations
- Cloud configuration reviews
- Vulnerability identification
- Data protection policy evaluations
- Regulatory compliance reviews
Design
- Unified, end-to-end security architecture design
- Cloud-native SIEM and SOAR design
- Security posture management for Azure resources
- Security and compliance rules development
- Secure storage and key management
- Endpoint security and mobile device management
Build
- Tool configurations aligned with best practices
- Integration for unified visibility
- Automation and orchestration
- Policy enforcement at scale
- Data protection in action
Improve
- Continuous tuning and optimization
- Policy and access reviews
- Compliance and risk monitoring
- Automation feedback loops
CYBERSECURITY CERTIFICATIONS
Your Elite Highly Trained Microsoft Team
More than 40% of our workforce consists of tenured cybersecurity engineers, architects and consultants. We are also highly certified across industry standards as well as hundreds of cybersecurity solutions.
Highly Trained, Highly Certified
Examples Include:









ADDITIONAL MICROSOFT SECURITY SERVICES
We Go Above and Beyond
Extend your Microsoft security capabilities with our specialized services, designed to address your complete technology lifecycle needs.
Migrations
Get tailored migrations that optimize performance, along with comprehensive documentation for streamlined operations.
Licensing
Let us help reduce costs, avoid overlap, ensure compliance and optimize investments.
Microsoft SME
Close the skills gap with GuidePoint’s Microsoft subject matter experts (SMEs) who integrate seamlessly into existing teams.
GuidePoint Microsoft Support
Get the most value out of support with rapid SME response and predefined SLAs.
Strategic Partnerships
Enhance and operationalize Microsoft environments through our strategic vendor partnerships that deliver innovation, improvement and growth.
Your Trusted Advisor
Our team works side-by-side with you as your cybersecurity partner.
“GuidePoint put a lot of effort into learning Intelsat – they got to know the people, they got to know our mission, they got to know our customers… They cultivated those relationships, they garnered that trust, not just with my senior leadership team, but also with the guys that are on the ground doing the work. Everyone looks at GuidePoint as a partner, not as a vendor.”
Vinit Duggal
Chief Security & Trust Officer at Intelsat

