The Rise of Infostealers: How Digital Identity Theft Fuels the Cybercrime Economy
This blog is brought to you by a research collaboration with our CTI colleagues and friends at LastPass. We hope that our combined analysis can help defenders mitigate damages caused by the plague of infostealers. You can also find this blog on the LastPass site HERE.
Executive Summary
Our lives are more online than ever, and our composite digital identities consist of a growing combination of social media, banking, shopping, and a myriad of other accounts, each guarded behind usernames and credentials which are tied to us. But what if someone could snatch our online identity using malicious software, or even use these stolen identities to move as a wolf in sheep’s clothing, granting them the access to extort individuals and organizations for millions of dollars? That is exactly the problem posed by information stealers, a threat which supports much of the cybercrime epidemic in ways seen and unseen. Information stealer malware, colloquially known as “infostealers”, have become a thriving business for fraudsters and a royal pain for defenders. In this blog, we’ll explore the infostealer economy, where they sit in today’s cybercrime ecosystem, and a recent example of how they were utilized in a publicized breach of a renowned organization.
What is an Information Stealer?
Before we can explore the impact of infostealers, it is beneficial to understand what they are and how they are used. Infostealers are a specialized form of malware designed to extract sensitive information from infected victim devices. The range of sensitive information worthy of extraction extends beyond just login credentials like usernames and passwords; modern infostealers can also compromise browser cookies and session tokens and use them to directly authenticate, take over a user’s active sessions, or bypass multi-factor authentication (MFA). Threat actors can then gain a direct entry point into a victim’s network or an individual’s entire digital identity. As if that wasn’t enough, contemporary infostealers are frequently capable of targeting cryptocurrency wallets, enabling the equivalent of digital bank robbery.
Once an infostealer infects a victim’s network and successfully collects a victim’s information, the malware generates a “log” file. A log is a digital dossier on the victim containing any and all sensitive information gathered from the user’s machine. In addition to stolen credentials, logs often include information on the operating system and installed software from a victim’s device, which threat actors can use to mimic an impacted computer using an “anti-detect” browser. Anti-detect browsers allow cybercriminals to circumvent anti-fraud protections organizations put in place, such as blocking unrecognized devices attempting to access an account for the first time.
Log files created by infostealers are often sold on dark web marketplaces at shockingly low prices – often as low as $10 USD. For cybercriminals selling these logs, this might be the only specialty they perform, exclusively focused on infecting and reaping the data of victims at scale. This allows for relatively easy profit with minimal risk and workload. Threat actors which focus on gaining and selling initial network access are called “Initial Access Brokers”, reflecting their specialized role within the cyber threat ecosystem, limited to a specific portion of the kill chain rather than full-spectrum intrusion expertise.
After infecting the victim’s system, an infostealer often remains running in the background, continually collecting and sending valuable data to the threat actor. The cybersecurity organization SpyCloud has noted that in the first half of 2024, 54% of the investigated infostealer infected devices also had anti-virus software or endpoint detection and response solutions in place, illustrating how effective infostealers can be even with traditional countermeasures in place. Infostealers may also be capable of loading additional malware on to the victim’s machine, either by the original actor or by a threat actor who has purchased the access. That additional malware can enable a more wide-ranging intrusion if the victim device belongs to a corporate network.
MaaS Model
Many infostealers operate under what is called a “Malware as a Service” (MaaS) model, in which a developer will create and maintain the underlying tool and infrastructure to provide product support once the infostealer malware is licensed to cybercriminal customers for use. Those customers can then use the infostealer to infect victims at will for the duration of their license.
The cybercriminal customers of infostealers may deliver the malware to victim devices in several ways, including:
- Creating websites that impersonate legitimate free software, or “cracked” commercial software, and packaging the infostealer within the download link, tricking users into installing the malware via a trojanized version of the impersonated software.
Threat actors artificially inflate their deceptive site’s ranking on search engines using Search Engine Optimization (SEO) poisoning techniques to ensure that the malicious pages rank near the top of a user search results, increasing the likelihood of successfully deceiving victims. Threat actors may purchase advertisements for the malicious pages with various search engines, a tactic known as “malvertising.” - Using phishing campaigns to reach wider audiences. Here, threat actors disguise the malware as a benign file and attach it to a seemingly legitimate email, depending on the inattention of the victim to open and execute an attached file. In a smaller minority of cases, such emails may be sent from compromised domain email addresses, leveraging the implicit trust of the sending domain to deceive the victim.
The nature of the Malware-as-a-Service (MaaS) model means there are no restrictions on how an actor may choose to infect their victims. Threat actors are constantly evolving their tactics and innovating new ways to trick their victims into clicking links, engaging in adversary social engineering foolery, executing suspect files, or blindly following instructions. We will continue to see novel techniques emerge for threat actors to compromise additional victim machines in the future.
Lucrative Business for All
Stolen credential sales may take place on simple social media or messaging platforms such as Telegram, but more frequently occur on illicit marketplaces such as “Russian Market”, secreted away in a corner of the deep and dark web.
Russian Market Login Page
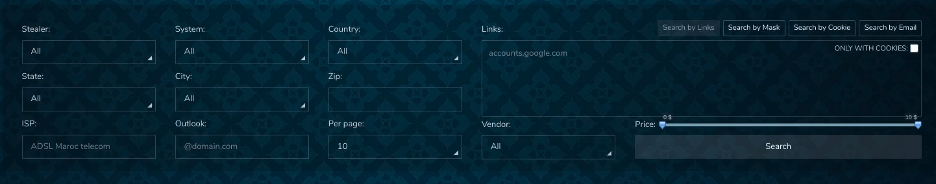
A single log could vary widely in terms of its usability and value for cybercriminals, containing data ranging from personal social media credentials to high-value financial login information or corporate network VPN credentials. Variance in quality contributes to low market prices for logs, which can be offered for as little as $10 USD – but this is a small price to pay for access to someone’s entire online identity. Russian Market allows prospective buyers to search for target logs in multiple ways, including the ability to search for information by targeted individuals or credentials for specific domains. This tactic can be used to target specific environments or infrastructure, as was likely demonstrated by 2024’s repeated attacks against Snowflake accounts resulting from compromised credentials.
Russian Market Search Filters
Essentially, today’s MaaS infostealer model and its supporting websites have transformed many threat actors into small business owners, settling into a cycle of licensing, compromising victims, and selling harvested information to generate a return on their investment. The relatively high cost of licensing and low revenue from log sales force operators to scale their operations quickly in order to turn a profit from their investment.
Infostealers Snowballing Out of Control
In May 2024, widespread breaches of cloud instances hosted by Snowflake sharply raised public awareness of the devastating effects of information stealing malware. What was originally reported as a breach of the cloud data platform Snowflake would come to instead reflect a much more complex scenario. Despite gaining access to data from over 160 organizations hosted by Snowflake, threat actors never attacked the Snowflake platform directly, as was originally reported. Rather, Mandiant identified that the actors targeted the poor security practices of the employees from the 160+ organizations. Attackers could have likely targeted each organization’s Snowflake accounts by searching for Snowflake-specific domains on Russian Market. Once the attackers obtained credentials for these specific domains, they were able to access massive amounts of data from the cloud instances of major organizations, leading to a reported $2.7 million in extortion attempts directed against these organizations. It is possible that a few infostealer logs bought for tens of dollars each could have been used by attackers to make millions in profit. Similar attacks have continued to affect organizations in the wake of the Snowflake breach. Credentials collected and dumped by infostealers remain a serious threat, especially for organizations that do not consistently monitor exposed credentials or have security measures like two-factor authentication in place. Starting in March 2025, the Hellcat ransomware gang breached multiple organizations using Jira credentials stolen from infostealer logs and leaked sensitive data. The hackers consolidated credentials from several infostealers including Lumma Stealer, Raccoon, Redline, and StealC, according to Hudson Rock. This relatively simple technique had a widespread impact, especially in this case given how centrally located Atlassian Jira is in enterprise workflows and the amount of sensitive data it houses. Once inside, threat actors can move laterally, escalate privileges, and extract critical information.
Hellcat targeted Schneider Electric, Telefónica, Orange Group, Jaguar Land Rover (JLR), and Ascom, among many others. In the case of the JLR incident, hackers used the credentials of an LG Electronics employee with third-party credentials to JLR’s Jira server. The compromised credentials were reportedly exposed for several years but remained valid, allowing hackers to take advantage. Given how widely available credentials collected by infostealers have become, alongside many organizations’ lacking account security practices, these attacks will continue to be an easy and effective way to gain unauthorized access moving forward, even for low-sophistication hackers.
What’s Next?
Server-side infostealers could serve as the next major advancement in infostealer malware. These were highlighted in an interview conducted by OSINT10x (which was echoed by Hudson Rock) with the malware developer behind Hellcat ransomware. Until now, infostealers have been client-side, meaning the malware is downloaded onto and executed entirely on a victim’s machine. In the case of a server-side infostealer, the victim’s machine only downloads a few lines of code. That code sets up a TOR server on the victim’s machine, which the threat actor can use to scrape for desired information via GET requests. This allows the threat actor to operate with a much lower profile and risk of exposure on the victim‘s machine. While this tactic hasn’t yet been widely adapted, it has the potential to spread rapidly against individuals and small to midsize businesses in particular that may not be configured to block TOR connections. This development could portend a shift towards lighter, quieter, and more capable infostealers. Getting in, executing on the victim’s machine, and exfiltrating the data as quickly and quietly as possible could be the name of the game in 2025.
What Can We Do?
Although it may seem like users and defenders are fighting a losing battle against the plague of information stealing malware, there are some actions that we can take to protect ourselves. Defenders can subscribe to quality threat feeds and implement them into their security stacks to guide security tooling with identifiers for new and evolving threats. These feeds can include hashes of the malicious software, as well as network indicators used by the malware. Indicators integrated into the proper tooling can detect or block the execution of a known infostealer, as well as, identify or prevent connection attempts to known Command and Control (C2) infrastructure, mitigating the exfiltration of any stolen credentials. Furthermore, threat feeds integrated with firewalls can prevent users from interacting with sites that may be hosting information stealing malware, as in the SEO poisoning and malvertising tactics discussed earlier, effectively preventing stealers from ever touching a user’s device.
Shifting to a reactive opportunity, defenders can also monitor the deep and dark web to detect whether any corporate credentials are being shared openly online. Security teams can utilize the same domain specific credential searches discussed above for defensive purposes. Early detection allows blue teams to identify if credentials have been stolen, potentially identifying and remediating the risk of compromised credentials before they can be exploited by threat actors.
Organizations can take strides to train employees in cybersecurity best practices, specifically on web search and password management. Training on the dangers of SEO poisoning and malvertising, can help better educate users to identify what is often the first element in the kill chain. In addition, informing users of the dangers of accessing corporate applications on personal devices can help limit this activity.
Lastly, encouraging employees to use legitimate password managers (such as LastPass!) instead of the heavily targeted vaults built into web browsers, can also mitigate some risk associated with infostealers. Employers may go so far as to encourage employees to use password managers on their personal devices, which could also contain sensitive corporate credentials.
GuidePoint Security Helps You Take Proactive Action Against Infostealers
For organizations seeking a robust, holistic approach to cybersecurity, GuidePoint Security offers tailored solutions that include end-to-end security architecture reviews, Identity and Access Management services, threat and attack simulation, penetration testing, and more. We empower you to protect your credentials against evolving threats so you can be better prepared against threats like those that led to the Snowflake breach.
Take control of your security today. Contact GuidePoint Security to learn how we can help safeguard your organization against credential-based attacks.